If you’ve recently come across the term Facebim, you’re not alone. The name has been appearing in online discussions, search queries, and niche digital communities, often without much clear explanation. That’s usually a sign that something new—or at least newly noticed—is taking shape.
This Facebim guide brings clarity. Instead of speculation or hype, you’ll get a grounded, practical look at what Facebim is, how it works in context, and why it’s gaining attention. Whether you’re researching it out of curiosity, business interest, or digital strategy, this breakdown will help you understand it with confidence.
What Is Facebim?
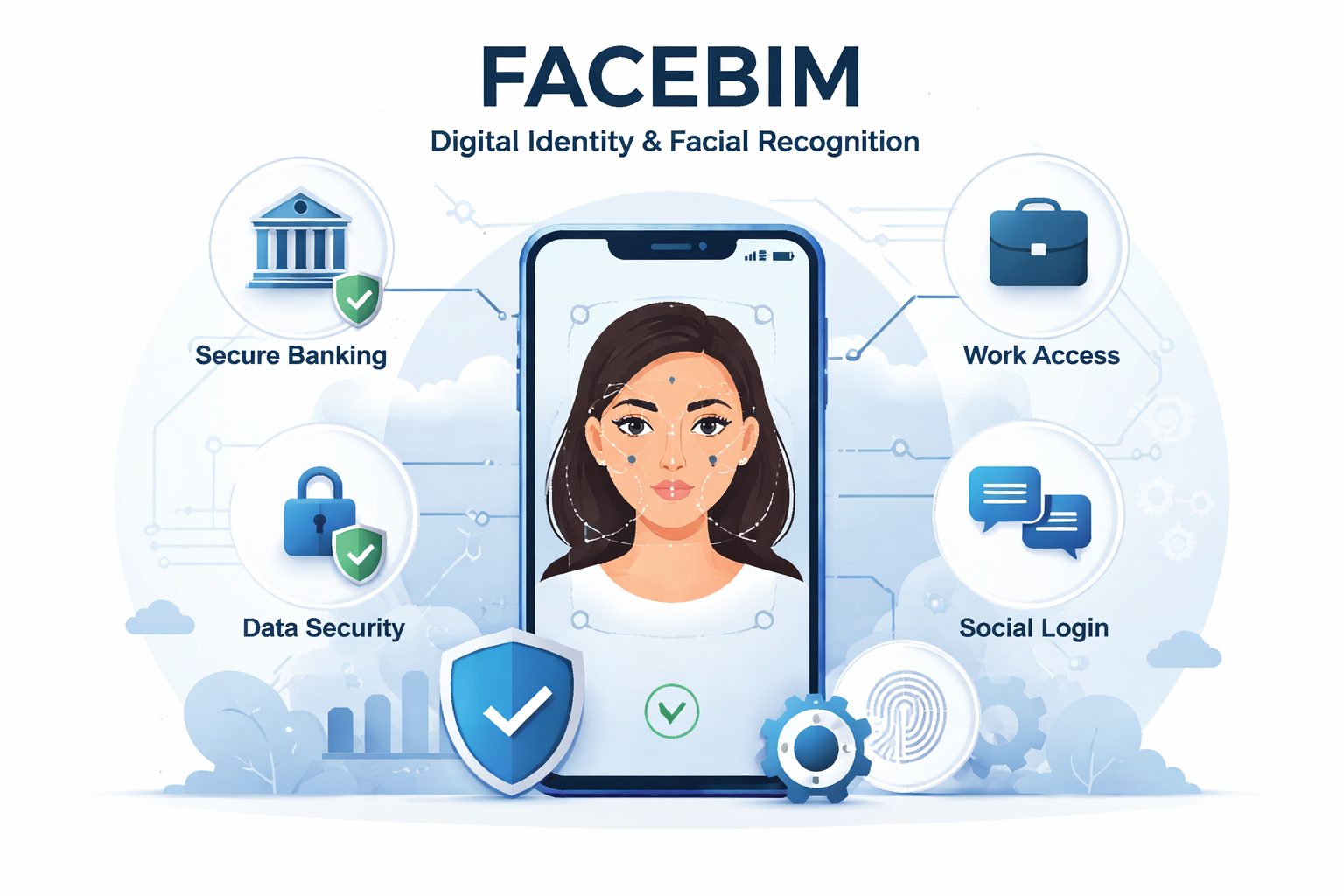
At its core, Facebim appears to be a digital identity-driven concept—one that combines elements of facial recognition, user verification, and online interaction within a single ecosystem.
The name itself suggests a blend of “face” (identity, recognition, presence) and a structured digital framework. While Facebim is not yet a universally standardized platform like Meta Platforms or a globally regulated biometric system, it reflects a broader shift happening online: identity is becoming more central to how we access, share, and interact.
In simple terms, Facebim represents a system—or idea—where face-based authentication or visual identity is linked to a digital experience. That could include:
- Login verification
- Secure account access
- Identity confirmation
- AI-based personalization
- Virtual profile presence
The exact implementation depends on context. In some cases, it may refer to a specific tool. In others, it may be a conceptual framework for identity-first digital systems.
Why Facebim Is Gaining Attention
Digital platforms have reached a point where usernames and passwords feel outdated. Security breaches, identity theft, and fake accounts have forced developers to rethink how trust is established online.
Face-based authentication already exists. Smartphones have normalized it. Apple’s Face ID changed expectations around security and convenience. Banking apps now use biometric layers as standard practice.
Facebim fits into this environment.
What makes it interesting isn’t just facial recognition itself. It’s the integration of identity with interaction. In many modern digital environments:
- You don’t just log in.
- You verify who you are.
- You establish authenticity.
- You link that authenticity to actions.
That layered identity model is what Facebim seems to represent.
How Facebim Works in Practice
While implementations may vary, Facebim systems generally rely on three core components:
1. Facial Data Capture
A camera captures facial features. This can be done through smartphones, webcams, or embedded device cameras.
The system maps unique facial points—distances between eyes, jawline structure, nose placement, and other biometric markers. These are converted into encrypted mathematical representations, not stored as simple photographs.
2. Secure Authentication Layer
The mapped data is stored securely, often encrypted and sometimes locally on the user’s device rather than on centralized servers.
When a user attempts access again, the system compares new scans to stored biometric signatures. If they match within defined thresholds, access is granted.
3. Integration with Digital Platforms
Here’s where Facebim becomes more than basic biometrics.
Instead of being limited to device unlocking, it may integrate with:
- Social platforms
- Financial services
- Virtual meeting systems
- Access control environments
- Digital workspaces
That’s where the concept expands from security tool to identity ecosystem.
Facebim vs Traditional Login Systems
Understanding Facebim is easier when you compare it to older systems.
| Traditional Logins | Facebim-Style Identity |
|---|---|
| Password-based | Biometric-based |
| Easily forgotten | Physically tied to user |
| Vulnerable to phishing | Harder to replicate |
| Anonymous-friendly | Identity-linked |
Passwords can be shared. Faces cannot.
That doesn’t automatically make Facebim superior in every context, but it shifts the balance toward authenticity and frictionless access.
Security Considerations and Privacy Concerns
Any system built around facial recognition raises legitimate questions.
Who stores the data?
Is it encrypted?
Can it be misused?
What happens if the database is breached?
These aren’t theoretical concerns. Biometric data is sensitive. Unlike passwords, you can’t change your face.
Responsible Facebim implementations should include:
- End-to-end encryption
- Local device storage where possible
- Explicit user consent
- Clear data retention policies
- Regulatory compliance (GDPR, etc.)
Context matters. In regions with strict privacy frameworks, Facebim-type systems must operate transparently. In loosely regulated spaces, caution is wise.
Users should always understand where their data lives and how it’s processed.
Real-World Use Cases of Facebim
Facebim-style systems can appear in several practical scenarios.
Digital Banking
Banks increasingly rely on facial verification for onboarding and transaction approval. This reduces fraud and eliminates dependency on physical branch visits.
Remote Work Environments
Identity confirmation during remote logins ensures that only authorized individuals access sensitive systems.
For companies handling confidential client data, this adds an extra verification layer beyond passwords or one-time codes.
Virtual Events and Online Communities
Authenticity has become a major issue online. Fake accounts undermine trust. Face-based identity confirmation can reduce impersonation in professional networks or paid communities.
Access Control Systems
Corporate offices and secure facilities already use facial access. Facebim can extend this logic to digital entry points.
Advantages of Facebim Systems
There’s a reason biometric systems continue to expand.
Convenience
You don’t need to remember anything. No password resets. No security questions.
Speed
Authentication takes seconds.
Reduced Fraud Risk
It’s far harder to replicate someone’s biometric signature than to guess a password.
Unified Identity
Instead of juggling multiple accounts and logins, Facebim systems can centralize identity management.
Limitations You Should Consider
It’s not perfect.
Lighting conditions can affect accuracy. Hardware quality matters. False positives and false negatives, though rare in advanced systems, are possible.
More importantly, biometric systems shift risk. If compromised, the impact is long-term.
There’s also the philosophical dimension. Some users simply prefer anonymity online. Facebim reduces that possibility in identity-linked ecosystems.
Adoption depends on user comfort, regulatory climate, and trust in the implementing organization.
Facebim and the Future of Digital Identity
Digital identity is moving toward verification, not just presence.
Platforms increasingly ask:
Are you real?
Are you human?
Are you who you claim to be?
CAPTCHAs were an early attempt to answer that. Two-factor authentication followed. Biometrics came next.
Facebim represents the convergence of identity, security, and interaction into one streamlined layer.
As AI-generated personas and deepfakes grow more sophisticated, systems like Facebim may become more common—not less.
However, adoption will likely remain contextual. Financial institutions and enterprise environments will lead. Casual platforms may adopt hybrid approaches.
Who Should Pay Attention to Facebim?
Facebim isn’t just for developers.
- Business owners exploring secure onboarding systems
- IT administrators managing remote teams
- Digital product builders designing login flows
- Privacy-conscious users evaluating new platforms
Understanding how identity systems evolve helps you make smarter decisions.
If you’re building or investing in digital infrastructure, identity authentication is no longer optional. It’s foundational.
Practical Tips Before Using a Facebim-Based Platform
If you’re considering joining or implementing a Facebim-enabled system, take a few practical steps:
- Read the privacy policy carefully.
- Check whether biometric data is stored locally or on external servers.
- Understand opt-out mechanisms.
- Confirm compliance with regional data laws.
- Evaluate whether biometric login is mandatory or optional.
Security isn’t about blind trust. It’s about informed trust.
Common Misconceptions About Facebim
“It stores actual photos of my face.”
Most secure systems convert facial features into encrypted biometric hashes, not simple image files.
“It’s 100% secure.”
No system is completely invulnerable. Risk is reduced, not eliminated.
“It replaces all other security layers.”
In well-designed ecosystems, biometrics complement—not replace—multi-layered protection.
FAQ: Facebim Guide
Is Facebim a specific app or a broader concept?
It can refer to a specific implementation, but often it represents a broader identity-based authentication framework using facial recognition technology.
Is Facebim safe to use?
Safety depends on how the system is built. Look for encryption standards, transparent data policies, and compliance with privacy regulations before trusting any platform.
Can Facebim be hacked?
While biometric systems are harder to exploit than passwords, no system is immune. Strong encryption and decentralized storage significantly reduce risk.
Do I lose anonymity if I use Facebim?
In identity-linked environments, yes. Facebim prioritizes verified presence over anonymous participation.
Is Facebim required for all platforms?
No. It’s typically optional or limited to platforms where high security or verified identity is essential.
Final Thoughts on Facebim
Digital identity is becoming more structured, more verified, and less anonymous. Facebim sits at that intersection of security and convenience. It’s neither a futuristic fantasy nor a universal solution. It’s part of an ongoing evolution in how we prove who we are online. Whether you view it as progress or a trade-off depends on what you value more: frictionless access or maximal privacy. What’s certain is this: identity is no longer just a username. And systems like Facebim are shaping what comes next.